Firefox
-
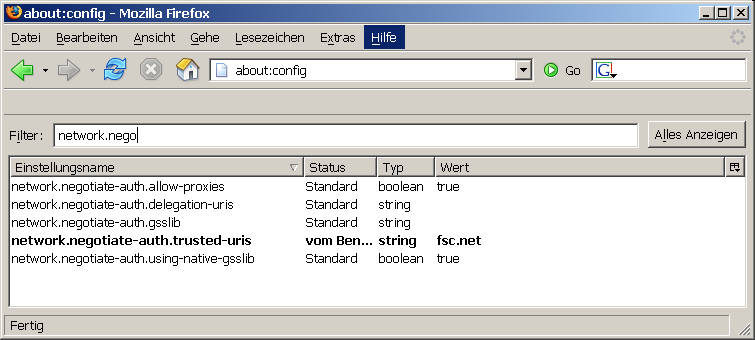
Start Firefox, enter
about:config
to the address field.
-
add the hostnames or domainnames you trust for delegation to the network.negotiate-auth.delegation-uris option
Internet Explorer (IE)
IE, authenticating against Active Directory (AD)
quoting Michael B Allen:
If you have auth working (and it's really doing Kerberos and not NTLM) then the only settings that could be responsible would be the two delegation settings:
-
In ADU&C [1] go to the Account tab of the service account used by mod_auth_kerb and make sure "Account is trusted for delegation" is checked. This is not set by default.
In ADU&C go to the Account tab of the User account for the client and make sure "Account is sensitive and cannot be delegated" is NOT checked. This is the default setting.
You can verify that the tickets the client has are Forwardable by running kerbtray.exe on the client. If the client's TGT is not Forwardable delegation will not occur and you need to find out why the TGT you're getting isn't Forwardable.
Additionally, some accounts will never do delegation. Administrator is one of them (in the wrong hands someone could do serious damage with Administrator's TGT - this is like 'root squash'). Even though the "Account is sensitive and cannot be delegated" flag is not on for Administrator it will still not do delegation. I believe this can be explained by looking at flags of the TGT in kerbtray but I'd have to check that on an XP machine and I'm feeling rather lazy right now :->
Mike[1] This assumes your Windows clients are joined to AD and not Heimdal or MIT. If the later is the case the concepts still apply, the settings are of course different.
-
-
IE, authenticating against Heimdal KDC
add attribute Heimdal attribute 'ok-as-delegate':
kadmin> modify HTTP/krb-server.int.oldboy Max ticket life [1 day]: Max renewable life [1 week]: Principal expiration time [never]: Password expiration time [never]: Attributes []:ok-as-delegate
Additonal IE-related ressources
KDE Konqueror
Konqueror does support GSSAPI, but not credentials delegation out of the box
get the kdelibs-x-y-z source package.
edit file
kioslave/http/http.cc
-
change
OM_uint32 req_flags = 0;
toOM_uint32 req_flags = GSS_C_DELEG_FLAG ;
Warning:this changes Konqueror to do always credentials delegation.
a configureable behaviour (for example based on target-hostname, like Firefox does) will be a lot better. Maybe someone adds a configuration dialog to Konqueror? A feature-request (ID 138414) is in KDEs bugzilla at http://bugs.kde.org/show_bug.cgi?id=138414